On Security Factors
This post should have a nicer title, but I can’t find it. It’s about security factors. In a way it might be a missing link between two of my talks: Passwords. Do you keep them safe? and CONTEXTVS, STVLTE!. And again, it’s somewhat ‘What did I just see here?!?’ driven, sometimes because my work, sometimes not ;-)
Passwords… Authentication… They were discussed so many times, you can find really many articles, thesis explaining, discussing, and comparing them. Not to mention dozens of cool and fancy advertisements that you’ll be safe, just use our product. So maybe this post is about these products…? And equality…? I’m not going to discuss égalité in general (along with liberté et fraternité). I’m not a mathematician, statistician or a cryptologist (that’s obvious, I’m not from Lviv), but I’ve been here and there and I saw things.

In my option the biggest threat to IT security in general is repeating and believing the mantra ‘oh, just do X, and you gonna be safe’. Examples? Here you go:
- your password needs to have big & small characters, numbers and special characters; if not, it’s rubbish
- single use passwords are the best passwords, no matter what
- using hardware tokens and biometrics should be used instead of passwords
- obscurity is security
- security is about doing something only once
- and so on.
P@ssw0rd
Let’s start with a P@ssw0rd. It’s an ever-green. Literally. We love green, we love to be green, go to the woods, have green builds, use green energy, have a lot of green papers, and see a green meter next to our password.
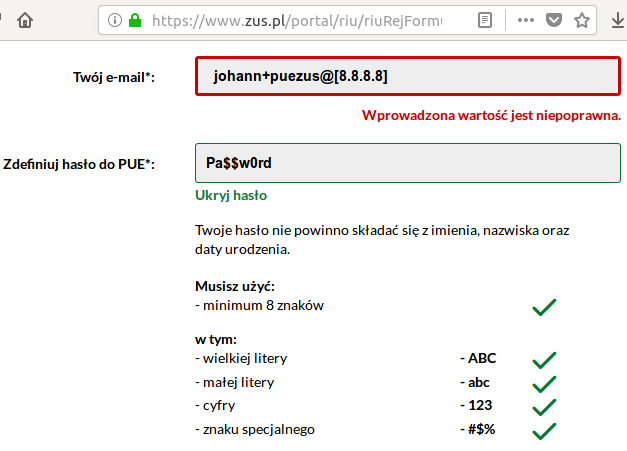
Question: is P@ssw0rd really a safe, unique password? Is it so difficult to guess? Dear full-stack developer, is your JS password strength meter, showing P@ssw0rd green, aware of dictionary attacks? Does it know that the joe@example.com has this very P@ssw0rd assigned in 17 other pages? Not quite? So why on Earth do you keep using these meters to fool the users, or worse, fool yourself, that this password is safe, because it has:
- a big letter => P
- a ‘special’ character => @
- a number => 0
Once again, I’m not sure if anything explains that better than the ‘correct horse battery staple’ strip.
That’s why forcing people to satisfy a regex with their password and get a green bar based on that might not be wise. Worse, if there’s a limitation on the password length (like 16 characters max), it’s stupid for sure, because it’s preventing people from using passwords easy to remember and with high guessing entropy.
Just this one time, baby
Single-use passwords are neat, aren’t they? What if I told you, my fellow developer, not always? If you have a list of pre-generated single-use passwords (and you really keep it secret), or your singe-use codes are generated by a nice hardware token, and they’re used when you have to log in to a system, that might be neat. It seems that you’re using a multi-factor authentication, nice. However, this is situational.
If you use the same mechanism not for authenticating yourself (confirming you are you), but let’s say, confirming a bank transfer (send XXX$ to YYY, pretty please), is it still that safe? Sure, a salesman will tell you ‘of course it is, our hardware token generates a unique key every X seconds, there’s a gazillion of combinations, impossible to guess, we’re synchronising this with a cesium atomic clock’ and so on. Then let me ask you this question: does this token show you to whom the money is going to be sent and how much?
The printed list/card of single-use codes can’t do that. Your hardware token showing only some codes can’t do that either. So if you’re really unlucky, it might be you’ve just entered your second-factor code in a page which looks like your bank, but it’s not, the super-duper-secure-second-factor single-use code just confirmed you’ve sent all your money far, far away.
Therefore, a single-use code, used as a second factor, is not equally safe in all situations. Because (surprise, surprise), the context is also needed. If it’s obvious and always the same (like authentication), good. If you use it in altering context without knowing the context, not equally good.
Give me a hand, please
If I was given a penny, just one penny, every time I hear or see ‘passwords are hard/old-fashioned/always insecure and should be replaced by biometrics or hardware’, I’d be at least a few pounds richer by now.
Adding one factor to another factor doesn’t sound bad in general. However, replacing one factor with another factor is another story.
Factors can be grouped in categories, e.g:
- something you know: a password, your wedding anniversary (you do remember that, right?), your dog’s name (c’mon, everyone knows it, Susan posted that on Facebook last summer, don’t you remember?), your swipe pattern
- something you have: a debit card, a piece of hardware, your fingerprints
They can be divided in other aspects too, like:
- something that can be changed or changes: a password, a sequence of characters generated somewhere
- something that cannot (easily) change: your birthdate, your social security number, your fingerprints (usually 10) (some research shows your fingerprints can change e.g. due to stress)
Some people just love counting. When they see anything having ‘factor’ in name, they just put a strong ‘check’ ✔️ next to it, then count the checks ✔️ and announce ‘we’ve implemented two-factor authentication, because we have two checks ✔️!’ Nope. If you use the same factor N times, it’s not an N-factor security. It’s still one factor, used N times, that’s it. So if you ask your customers their password AND their birthdate, it’s not 2FA. To have a multi-factor authentication, you need to have multiple types of factors, not the same kind of factor repeated many times.
Sometimes one factor gets replaced by another and such replacement is justified more or less by ‘people are weak at X, so let’s replace it with Y’. Many times we want such replacement, because one factor is more convenient to use. Having a smartwatch on your wrist or swiping a finger on a reader is much easier than entering a (masked) password after all.
However, there might be one more ways the security factors can be divided:
- things that can be ‘taken’ from you and you don’t even notice: your password (if you wrote it on a sticker or if it’s simple to guess), your SSN, name of your dog
- things that can be ‘taken’ from you when you’re unconscious: your phone, your fingerprints, your phone which can be unlocked by your fingerprint (even when you’re dead)
- things that cannot be taken from you without you knowing it: your password (if you keep it in your brain only)
I wish I could add ‘things that cannot be taken from you in any way’, but there’s always a baseball bat attack vector or drugs. There’s one more obvious point though:
- things that cannot be taken from you when you’re no more: things only you know (like memorised password).
It’s not my intention to put you in a situation when you have to experience such hard choices, but maybe it’s worth thinking about such dilemmas, because being aware of them doesn’t harm. Especially, when it’s about trading security (and maybe chances of being kept alive) with convenience, because it might not always be about terminal situations. Being robbed, because your smartwatch opened the Sesame, being arrested and groundlessly accused because your phone ‘testified something’, etc. I know there are attempts in some law systems here and there to make revealing your password obligatory, but I guess it might be still legal to forget the password due to some stress.
That’s why I dare to say
Not all security factors are equal
Just because people use weak passwords (the green meter again), it doesn’t mean automatically, that the what-I-have factor is ultimately better that the what-only-I-know factor. Or because aggressive marketing tells you so.
Maybe Jinx & 007 can explain that better than I do ;-)
Stay safe, folks.
